Click on the "New" button at the top of the VirtualBox Manager window. A wizard will pop up to guide you through setting up a new virtual machine (VM):
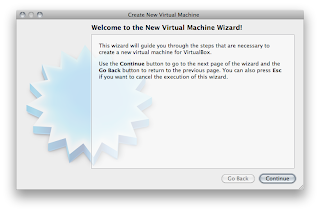
On the following pages, the wizard will ask you for the bare minimum of information that is needed to create a VM, in particular:
1. The VM name will later be shown in the VM list of the VirtualBox Manager window, and it will be used for the VM's files on disk. Even though any name could be used, keep in mind that once you have created a few VMs, you will appreciate if you have given your VMs rather informative names; "My VM" would thus be less useful than "Windows XP SP2 with OpenOffice".
2. For "Operating System Type", select the operating system that you want to install later. The supported operating systems are grouped; if you want to install something very unusual that is not listed, select "Other". Depending on your selection, VirtualBox will enable or disable certain VM settings that your guest operating system may require. This is particularly important for 64-bit guests (see the section called “64-bit guests”). It is therefore recommended to always set it to the correct value.
3. On the next page, select the memory (RAM) that VirtualBox should allocate every time the virtual machine is started. The amount of memory given here will be taken away from your host machine and presented to the guest operating system, which will report this size as the (virtual) computer's installed RAM.
Note: Choose this setting carefully! The memory you give to the VM will not be available to your host OS while the VM is running, so do not specify more than you can spare. For example, if your host machine has 1 GB of RAM and you enter 512 MB as the amount of RAM for a particular virtual machine, while that VM is running, you will only have 512 MB left for all the other software on your host. If you run two VMs at the same time, even more memory will be allocated for the second VM (which may not even be able to start if that memory is not available). On the other hand, you should specify as much as your guest OS (and your applications) will require to run properly.
A Windows XP guest will require at least a few hundred MB RAM to run properly, and Windows Vista will even refuse to install with less than 512 MB. Of course, if you want to run graphics-intensive applications in your VM, you may require even more RAM.
So, as a rule of thumb, if you have 1 GB of RAM or more in your host computer, it is usually safe to allocate 512 MB to each VM. But, in any case, make sure you always have at least 256 to 512 MB of RAM left on your host operating system. Otherwise you may cause your host OS to excessively swap out memory to your hard disk, effectively bringing your host system to a standstill.
As with the other settings, you can change this setting later, after you have created the VM.
4. Next, you must specify a virtual hard disk for your VM.
There are many and potentially complicated ways in which VirtualBox can provide hard disk space to a VM (see Chapter 5, Virtual storage for details), but the most common way is to use a large image file on your "real" hard disk, whose contents VirtualBox presents to your VM as if it were a complete hard disk. This file represents an entire hard disk then, so you can even copy it to another host and use it with another VirtualBox installation.
The wizard shows you the following window:
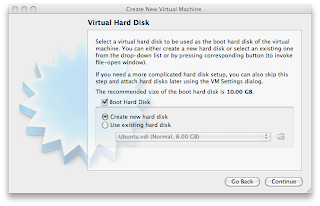
Here you have the following options:
* To create a new, empty virtual hard disk, press the "New" button.
* You can pick an existing disk image file.
The drop-down list presented in the window contains all disk images which are currently remembered by VirtualBox, probably because they are currently attached to a virtual machine (or have been in the past).
Alternatively, you can click on the small folder button next to the drop-down list to bring up a standard file dialog, which allows you to pick any disk image file on your host disk.
Most probably, if you are using VirtualBox for the first time, you will want to create a new disk image. Hence, press the "New" button.
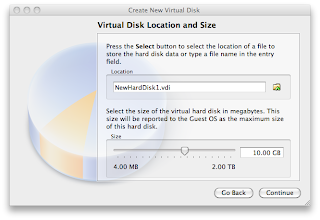
This brings up another window, the "Create New Virtual Disk Wizard", which helps you create a new disk image file in the new virtual machine's folder.
VirtualBox supports two types of image files:
* A dynamically allocated file will only grow in size when the guest actually stores data on its virtual hard disk. It will therefore initially be small on the host hard drive and only later grow to the size specified as it is filled with data.
* A fixed-size file will immediately occupy the file specified, even if only a fraction of the virtual hard disk space is actually in use. While occupying much more space, a fixed-size file incurs less overhead and is therefore slightly faster than a dynamically allocated file.
For details about the differences, please refer to the section called “Disk image files (VDI, VMDK, VHD, HDD)”.
To prevent your physical hard disk from running full, VirtualBox limits the size of the image file. Still, it needs to be large enough to hold the contents of your operating system and the applications you want to install -- for a modern Windows or Linux guest, you will probably need several gigabytes for any serious use:
After having selected or created your image file, again press "Next" to go to the next page.
5. After clicking on "Finish", your new virtual machine will be created. You will then see it in the list on the left side of the Manager window, with the name you entered initially.
Running your virtual machine
To start a virtual machine, you have several options:
* Double-click on its entry in the list within the Manager window or
* select its entry in the list in the Manager window it and press the "Start" button at the top or
* for virtual machines created with VirtualBox 4.0 or later, navigate to the "VirtualBox VMs" folder in your system user's home directory, find the subdirectory of the machine you want to start and double-click on the machine settings file (with a .vbox file extension).
This opens up a new window, and the virtual machine which you selected will boot up. Everything which would normally be seen on the virtual system's monitor is shown in the window, as can be seen with the image in the section called “Some terminology”.
In general, you can use the virtual machine much like you would use a real computer. There are couple of points worth mentioning however.
Starting a new VM for the first time
When a VM gets started for the first time, another wizard -- the "First Start Wizard" -- will pop up to help you select an installation medium. Since the VM is created empty, it would otherwise behave just like a real computer with no operating system installed: it will do nothing and display an error message that no bootable operating system was found.
For this reason, the wizard helps you select a medium to install an operating system from.
* If you have physical CD or DVD media from which you want to install your guest operating system (e.g. in the case of a Windows installation CD or DVD), put the media into your host's CD or DVD drive.
Then, in the wizard's drop-down list of installation media, select "Host drive" with the correct drive letter (or, in the case of a Linux host, device file). This will allow your VM to access the media in your host drive, and you can proceed to install from there.
* If you have downloaded installation media from the Internet in the form of an ISO image file (most probably in the case of a Linux distribution), you would normally burn this file to an empty CD or DVD and proceed as just described. With VirtualBox however, you can skip this step and mount the ISO file directly. VirtualBox will then present this file as a CD or DVD-ROM drive to the virtual machine, much like it does with virtual hard disk images.
For this case, the wizard's drop-down list contains a list of installation media that were previously used with VirtualBox.
If your medium is not in the list (especially if you are using VirtualBox for the first time), select the small folder icon next to the drop-down list to bring up a standard file dialog, with which you can pick the image file on your host disks.
In both cases, after making the choices in the wizard, you will be able to install your operating system.
Capturing and releasing keyboard and mouse
As of version 3.2, VirtualBox provides a virtual USB tablet device to new virtual machines through which mouse events are communicated to the guest operating system. As a result, if you are running a modern guest operating system that can handle such devices, mouse support may work out of the box without the mouse being "captured" as described below; see the section called “"Motherboard" tab” for more information.
Otherwise, if the virtual machine only sees standard PS/2 mouse and keyboard devices, since the operating system in the virtual machine does not "know" that it is not running on a real computer, it expects to have exclusive control over your keyboard and mouse. This is, however, not the case since, unless you are running the VM in full-screen mode, your VM needs to share keyboard and mouse with other applications and possibly other VMs on your host.
As a result, initially after installing a guest operating system and before you install the Guest Additions (we will explain this in a minute), only one of the two -- your VM or the rest of your computer -- can "own" the keyboard and the mouse. You will see a second mouse pointer which will always be confined to the limits of the VM window. Basically, you activate the VM by clicking inside it.
To return ownership of keyboard and mouse to your host operating system, VirtualBox reserves a special key on your keyboard for itself: the "host key". By default, this is the right Control key on your keyboard; on a Mac host, the default host key is the left Command key. You can change this default in the VirtualBox Global Settings. In any case, the current setting for the host key is always displayed at the bottom right of your VM window, should you have forgotten about it:
Next


